Fraud Awareness

E-Transfer Interception
E-transfer interception can occur when a fraudster gains unauthorized access to an e-transfer recipient’s email account or phone number. By gaining this access, the fraudster can use the deposit link to redirect funds into a different account, if they are able to answer the security question.

Email Safety
What if you are hacked?
You might have been hacked if:
- Friends and family are getting emails or messages you didn’t send.
- Your 'Sent' messages folder has messages you didn’t send, or it has been emptied.
- Your social media accounts have posts you didn’t make.
- You can’t log into your email or social media account.

Investment Fraud
Ten Self-Defense Tips
Investment fraud schemes, sometimes referred to as high yield investment fraud, involve the illegal sale or purported sale of financial instruments. Schemes take on many forms, and perpetrators quickly alter schemes as they are thwarted by law enforcement.

Phone Scams
DO NOT FALL FOR PHONE SCAMS
Many people lose a lot of money to phone scams – sometimes their entire life savings. Phone scams can take many forms, but the fraudsters always have the same objective – get your money or get your personal information to commit identity theft. To do this, scammers may act friendly and helpful or they might threaten or try to scare you. Since they usually follow similar patterns it’s important to familiarize yourself with how to identify a phone scam.

Romance Scams
Romance scams occur when a criminal adopts a fake online identity to gain a victim’s affection and trust. The scammer may chat back and forth with their victim for weeks, even months to form a connection. The criminal may also send flowers or gifts to further form the illusion of a romantic or close relationship. But ultimately, this new-found “friend” will ask their victim for money.

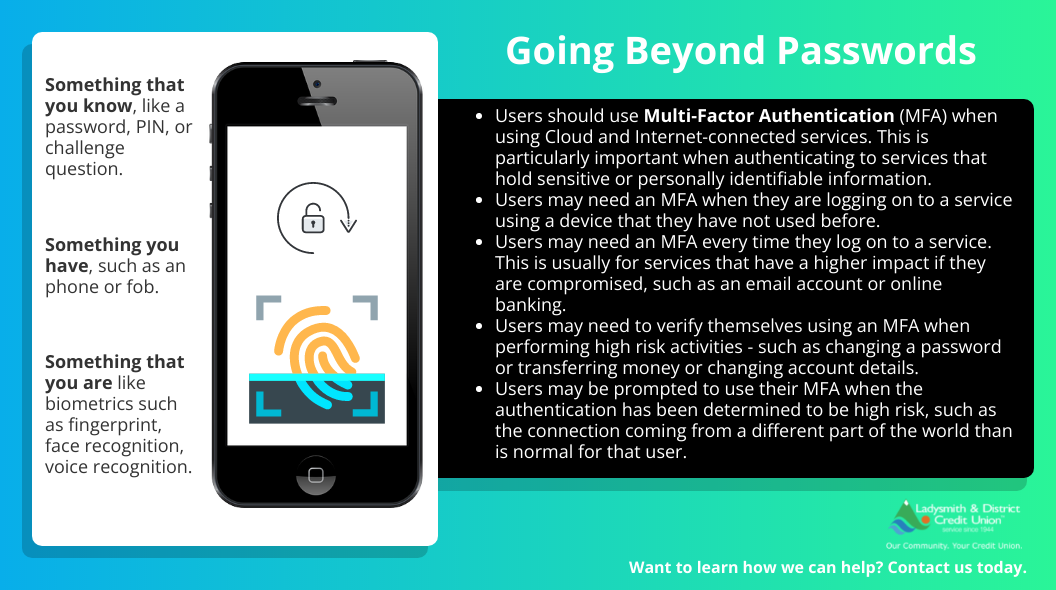
Mobile Device Security
Password - Tips to Prevent Fraud
Passwords can only do so much. Even when implemented correctly, passwords are limited in helping prevent unauthorised access. If an attacker discovers or guesses the password, they are able to impersonate a user.